In the modern cyber threat landscape, supply chain attacks have emerged as one of the most effective attack vectors. Attackers exploit integrations between systems—such as software distribution, cloud services, and software dependencies—to gain initial access without having to directly exploit vulnerabilities. The 2022 study “Supply Chain Characteristics as Predictors of Cyber Risk” shows that this approach significantly increases the probability of cyber incidents as the complexity of the digital ecosystem grows.

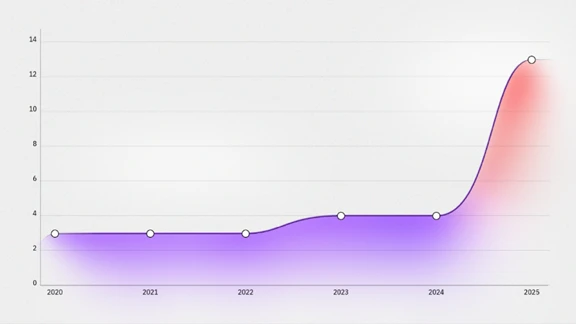
The IBM X-Force Threat Intelligence Index 2026 report indicates that supply chain compromise incidents have increased nearly fourfold over the past five years.
This trend reflects a shift in attacker strategies that leverage trusted integrations as a pathway for initial access, enabling attacks to spread systematically and impact multiple entities within a single distribution chain. This is further reinforced by Group-IB’s High-Tech Crime Trends Report 2026, which identifies that various threat actors—such as Lazarus, Scattered Spider, HAFNIUM—as well as criminal groups like DragonForce and 888—are actively leveraging supply chain attacks in their operations.
One example of a supply chain attack is the campaign within the NPM ecosystem linked to Shai-Hulud, where the threat actor injects malicious code into packages or publishes modified versions. When the package is installed, the malicious code is automatically executed to steal credentials such as GitHub tokens, NPM tokens, and cloud access credentials. These credentials are then used to infect other packages, allowing the attack to spread widely within the ecosystem.
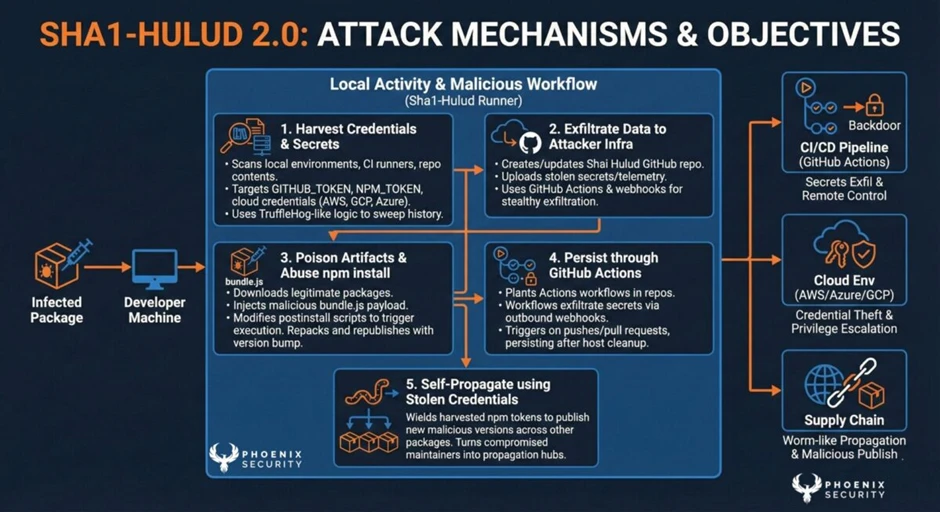
A key characteristic of a supply chain attack is its ability to disguise malicious activity as part of normal processes. Since such activity appears legitimate (normal) in system logs and monitoring, many conventional security controls fail to detect the attack in its early stages. This situation allows threat actors to maintain access, perform lateral movement, and expand their control undetected for extended periods.
The impact of a supply chain attack is not merely technical but also directly affects an organization’s operations, finances, and reputation. Therefore, this risk must be viewed as a strategic issue at the management level. In response, organizations need to adopt a security approach focused on enhancing visibility and control over distribution channels and system integrations, as well as implementing the Zero Trust principle, where every process must be verified in real-time to be classified as secure.
References:
https://arxiv.org/abs/2210.15785
https://www.ibm.com/reports/threat-intelligence
https://www.ibm.com/think/insights/more-2026-cyberthreat-trends
https://www.enisa.europa.eu/publications/threat-landscape-for-supply-chain-attacks
https://www.group-ib.com/media-center/press-releases/htct-2026-supply-chain/
https://jfrog.com/blog/shai-hulud-npm-supply-chain-attack-new-compromised-packages-detected/
https://phoenix.security/shai-hulud-campaign-timeline/

