
More than three weeks into the U.S.-Israel war with Iran, we are stunned to see that the mechanics of the attacks have shifted toward mutually destructive forces. The sheer number of troops is no longer the decisive factor; instead, supporting technology with the latest attack models is key: AI, drones, and satellites—which serve as both monitors and target guides—have become paramount. Additionally, the use of stealth technology and radar jamming techniques has made us realize how modern warfare is gradually evolving. The image above was taken on March 15, 2026, during an episode of *The Big Weekend Show* on Fox News. Social media has been abuzz in recent days following widespread netizen speculation that a U.S. aircraft carrier was successfully damaged by Iran, culminating in a video of the Israeli Prime Minister that is alleged to be an AI-generated image.
In research ranging from (Robinson, Jones, & Janicke, 2015) to the latest studies by (Kilincer, Ertam, & Sengur, 2021), (Hasan et al., 2023), (Vennela, Akarapu, Rakshith, Asirvatham, & Sunil, 2026) explain the handling of cyberattacks, particularly issues related to cyberwarfare, malware, and other dark web activities on the Internet. Currently, cyberattacks are becoming increasingly diverse, with widespread and severe impacts, compounded by the ease of accessing hacking tools that possess comprehensive destructive features without requiring expertise in coding or networking.
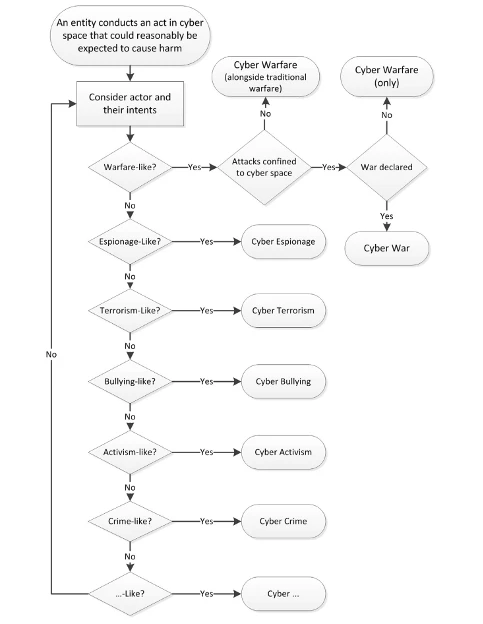
Figure 1: Hierarchy of Warfare Types (Robinson et al., 2015)
Cyber warfare has entered a new era, where a nation, supported by its resources, attempts to penetrate another nation’s computers or networks with the aim of causing massive damage or disruption, particularly targeting public services. As illustrated in Figure 1 presented by Robinson, this depicts the flow of steps or decisions used to categorize actions resulting from or occurring during a conflict.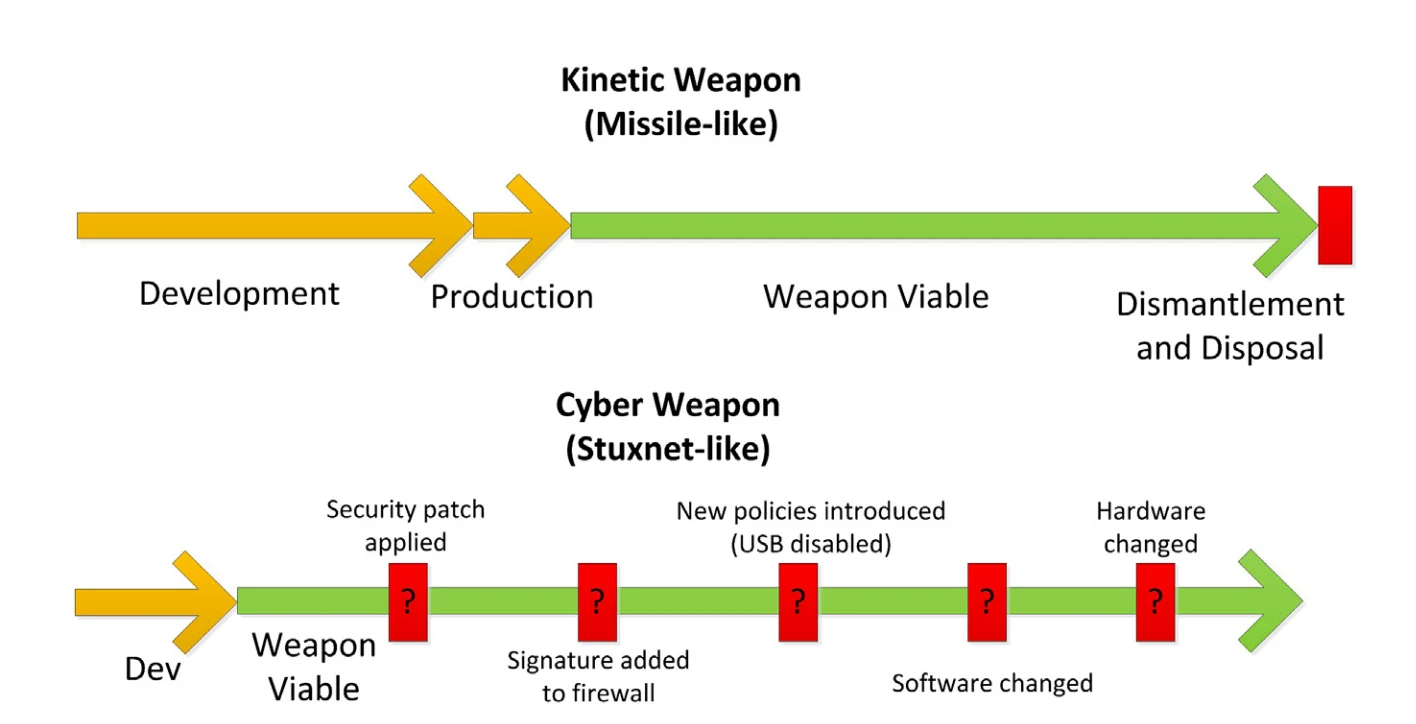 Figure 2: Weapons Life Cycles (Robinson et al., 2015)
Figure 2: Weapons Life Cycles (Robinson et al., 2015)
Figure 2, presented by Robinson, illustrates two attack models in the event of a military war between nations. It is evident that such scenarios are currently unfolding, ranging from conventional attacks using guided ballistic missiles to drones capable of striking precise targets from thousands of kilometers away from their launch points. This extends to hacking assets through information interception on interconnected telecommunications resources or central command systems by implanting malware to track and intercept passing information, followed by subsequent actions such as: remote backdoors, man-in-the-middle attacks, and so on.
In the current situation, as outlined in the editorial (Michael, Herold, & Roussos, 2026), Deepfakes have become an integral part of cyberwarfare, likely reshaping the landscape of warfare. AI-generated deepfakes have been used to manipulate public opinion by easily creating news and spreading it massively on social media. Thus, deepfakes will become a major issue in the future, particularly in information warfare, where parties vie to claim victory and highlight progress achieved.
References
Hasan, M. K., Habib, A. K. M. A., Shukur, Z., Ibrahim, F., Islam, S., & Razzaque, M. A. (2023). Review on cyber-physical and cyber-security systems in smart grids: Standards, protocols, constraints, and recommendations. Journal of Network and Computer Applications, 209, 103540. doi:https://doi.org/10.1016/j.jnca.2022.103540
Kilincer, I. F., Ertam, F., & Sengur, A. (2021). Machine learning methods for cyber security intrusion detection: Datasets and comparative study. COMPUTER NETWORKS, 188, 107840. doi:https://doi.org/10.1016/j.comnet.2021.107840
Michael, K., Herold, R., & Roussos, G. (2026). Security and regulation: Cybersecurity, privacy, and trust—protecting information and ensuring responsible technology use. Computers & Security, 162, 104804. doi:https://doi.org/10.1016/j.cose.2025.104804
Robinson, M., Jones, K., & Janicke, H. (2015). Cyber warfare: Issues and challenges. Computers & Security, 49(0), 70-94. doi:http://dx.doi.org/10.1016/j.cose.2014.11.007
Vennela, A., Akarapu, R. B., Rakshith, B. L., Asirvatham, L. G., & Sunil, G. (2026). Intelligent cybersecurity systems for phishing attack detection - An overview. Computers and Electrical Engineering, 130, 110829. doi:https://doi.org/10.1016/j.compeleceng.2025.110829

